Opinion
Could Blockchain Hold the Answer for IoT’s Security Issues?
“Security is a critical element of IoT deployment, yet it is too often neglected in the development of systems.” — Internet of Things Security Foundation (IoTSF)
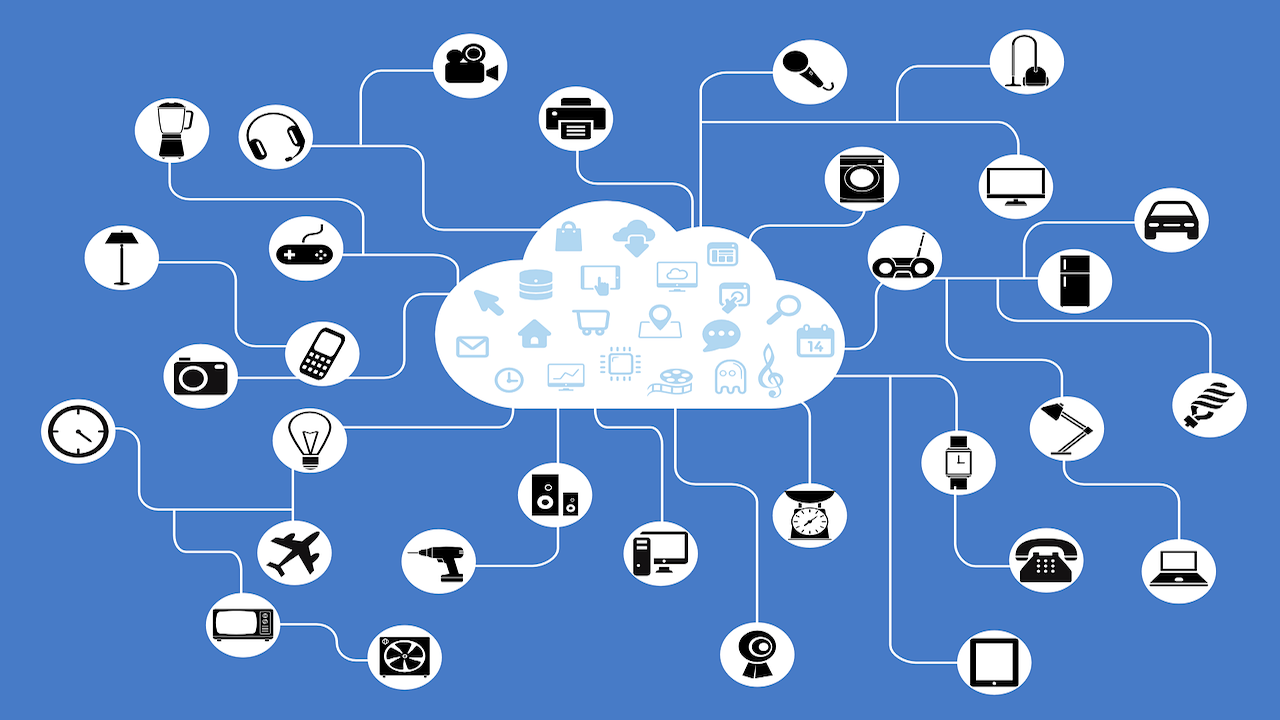
When you think about what’s possible today thanks to the rise of the Internet of Things (IoT), you might start to feel like you’re in an episode of the Jetsons. Smart homes are increasingly popular, and that’s just touching on its considerable promise. But there’s a problem; it’s been there all along, but as IoT adoption expands, the need for a solution is growing more urgent: Security.
Here’s a scenario that could make your heart skip a beat — perhaps literally. If someone with nefarious intentions gains access to your IoT platform, they would be able to control the array of devices connected to it: thermostats, door locks, digital cars, kitchen appliances, microphones, and even medical devices — including pacemakers.
And consider this: the Pew Research Center reports that Elon Musk, among others, has announced plans to create a brain-computer interface available for consumer use.
Think that’s scary? That’s just the beginning. It’s not just your car or your brain. IoT adoption by governments and multinational companies has elevated the potential impact of security breaches.
“In the mainstream press, IoT is regularly depicted as Internet-connected washers and dryers or fitness trackers,” FedTech Magazine observes. But the reality is far more expansive. “Agencies are taking IoT seriously and putting it to more practical uses.”
For example, Government Technology reports that Los Angeles has 145,000 streetlights and 4,500 intersections controlled via IoT technology.
This means public infrastructures — traffic lights, transportation, water services and power plants — could be vulnerable, reports Network World. “This raises the stakes for adequate cyber security considerably, as a compromised system has much larger consequences than the organization losing profitability and efficiency.”
Add military installations to the list. A disturbingly recent (July 2017) report from the Government Accountability Office has found that the Defense Department isn’t doing enough. Specifically, it reported that the DoD’s policies on Internet of Things devices aren’t adequate to protect against the potential security risks.
Ripe for Attack
One thing is clear: The Internet of Things is ripe for cyberattacks. Symantec points out that weak security makes these IoT devices easy targets, and as a result, the number of attempted attacks against IoT devices doubled in 2016.
The barrier to entry for creating an IoT product is relatively low, and the security protocols on these devices and the apps that control them vary widely.
“There is little consideration of the fact that if IoT devices are deliberately made so that they can perform functions remotely, they can also spy on their owner and relay personal data back to a central collection point,” according to the authors of Internet of things: pinning down the IoT, a report from F-Secure.
That’s also what a January 2018 piece from Information Age suggests.
“But with the IoT bandwagon rushing full steam ahead, few vendors or customers are pausing to consider the enormous security risks associated with the devices. The influx of additional entry points into an organization’s network, plus a current lack of security standards for IoT devices, means there is a gaping hole in the perimeter of any home or business that has installed IoT devices.”
But the bandwagon is unlikely to slow down, so the only option is to find a solution. That requires, first, understanding the nature of the problem.
It’s important to note that different IoT devices and applications have different security goals. You might need to prevent tampering or keep information private. These are both security goals, but they are very different problems with different solutions. Blockchain has the potential to prevent IoT data tampering.
Centralization is the Achilles’ Heel for Tampering
IoT platforms are typically architected using a centralized model in which a hub controls the interaction among devices. Devices are identified, authenticated and connected through cloud servers. That means that even if the devices are in the same house — even sitting next to each other on your kitchen counter, the connection has to go through the central hub. This is what make it easier to hack and tamper with.
But although centralization is the core issue, but there are related factors contributing to the risk.
- More devices mean more risk: Obviously. And there will be more: Gartner predicts more than 20.4 billion “connected things” will be in use by 2020, compared to 6.4 billion in 2016.
- We’ve become more dependent: It’s not just the number of devices, but how they have become so integrated into our lives. “As the Internet of Things continues to grow and have a greater impact on daily life, for both consumers and enterprises, the temptation to attack it for malicious purposes will also continue to grow,” according to a Security Analytics report.
- Speed kills — or at least impairs — security: Companies pushing IoT devices out quickly end up compromising on security, according to a CSO article. Even if they offer upgrades, they don’t do so indefinitely, and consumers have “slightly outdated hardware” that can become a more-than-slight security risk. “These companies sometimes have the intention of fixing a vulnerability like that through a firmware upgrade, but then never get around to it because they don’t want to disrupt the user base,” Craig Young, a cybersecurity researcher at Tripwire, tells the publication.
All of this means what was effective yesterday won’t work today.
Current Approaches are Obsolete
Traditional security solutions will not be effective in protecting these devices, warns a Harvard Business Review piece — appropriately titled “The Internet of Things Is Going to Change Everything About Cybersecurity.” It notes, for instance, that attacks on IoT devices were up 280 percent in the first half 2017.
Clearly, the security protecting the IoT from such breaches is relatively limited. Mostly, it’s just your ID, plus a password and perhaps a two-factor authorization protocol. The former is inadequate, the latter is an inconvenience and may still be inadequate.
One solution under development, biometrics, is promising. Facial and voice recognition, fingerprints could offer a solution. But the technology for biometric verification is far from perfect, according to Hacker Noon. It could be hacked, or, perhaps even worse, the people who should have access could be locked out.
Current solutions aren’t working, according to the experts. Leveraging blockchain just might. A recent CB Insights report doesn’t hedge on this point: “If blockchain is more widely adopted, the probability of hacking could go down, as the cyberprotections of the technology are more robust than legacy systems.”
Turning to Blockchain
If one of the greatest challenge facing IoT security relates to its centralized architecture, then blockchain is the ideal solution, explains IoT expert Ahmed Banafa. “The decentralized, autonomous, and trustless capabilities of the blockchain make it an ideal component to become a foundational element of IoT solutions.”
Instead of layering on levels of security and authentication, it allows security to be distributed.
Blockchain can be used in tracking billions of connected devices and allow for coordination between those devices, rather than through a central hub, improving security and saving money, Banafa continues. “This decentralized approach would eliminate single points of failure, creating a more resilient ecosystem for devices to run on.”
Forget IoT for a moment and just think about how blockchain supports cybersecurity. Blockchain reduces risk by removing the need for intermediaries, thereby minimizing the possibility of hacking, malfeasance, or simple human error. Transactions are “peer to peer,” not mediated.
This decentralization means there’s no potential single point of failure, and there’s no centralized repository for a hacker to access. That doesn’t mean it can’t be altered. It’s just a lot harder. To tamper with one record, the hacker would have to hack all nodes worldwide and change the information in all computers simultaneously. It would be hard to do that unnoticed, and the sheer computational power required would be extraordinary, experts say.
However, when it comes to IoT, it’s not so simple. A “family” of devices typically requires a central control codebase to provide the proper business logic for the devices, whether it lives on one server, or is made to be distributed across the devices. If that doesn’t change in the future, there could still be a central point of attack on a blockchain-based network. There is still a lot of research and testing needed about the intersection of blockchain and IoT and the best way to combine the two technologies.
Beyond Security
Even apart from the security concerns, this approach is impractical — it would simply make more sense for devices to exchange data among themselves directly. As Martha Bennett, principal analyst at Forrester Research, points out, for IoT to live up to its potential, devices will eventually communicate “directly, autonomously, and securely with each other.”
Without a central control system, the devices would be able to communicate with one another autonomously to manage updates, bugs, energy management, etc. The current centralized model would become obsolete, predicts Banafa.
Making Progress
Startups and incumbents alike are looking to build blockchain technology into an IoT platform, according to an August 2017 report from CB Insights.
As an example of the former, CB Insights cites Filament, which developed a decentralized network for IoT that allows IoT sensors to communicate directly with each other without going through a central intermediary.
As for the incumbents, IBM and Samsung are collaborating on ADEPT (Autonomous Decentralized Peer-to-Peer Telemetry), which uses blockchain-type technology to form the backbone of a decentralized network of IoT devices.
Ericsson Research demonstrated a proof-of-concept for integrating and securing IoT devices from any ecosystem at the 2017 Mobile World Congress.
Challenges to Blockchain
Blockchain may offer a solution, but getting there from here will not be easy. Banafa and others have identified several challenges. Among them:
- Scalability: This is, of course, a known issue for blockchain applications, and it will pose a particular challenge for IoT. Currently, blockchain scales poorly as the number of nodes in the network increases, and IoT networks are expected to contain an extremely large number of nodes, point out researchers from the University of New South Wales.
- Processing power and time: Encryption and verification of blockchain transactions are computationally intensive operations and, as TechCrunch puts it, “require considerable horsepower to carry out, which is lacking in many IoT devices.” In fact, as the Hacker Moon piece notes, the IoT ecosystem includes devices with widely varying sizes of computing capabilities.
- Shortage of developers: There’s already a shortage of blockchain developers. The pool of those with both blockchain and IoT expertise is, of course, even smaller.
- Lack of legal guidance: If you’ve been following blockchain at all, you know it’s been called everything from the “wild, wild west” to a “brave new world.” The law has yet to catch up. “This challenge alone will scare off many businesses from using Blockchain technology,” warns Banafa.
Hot, Warm, and Cold: Opinions Vary
“IoT security is not a finite process, but one that should be viewed as an ongoing process that will continually need to deal with unforeseen eventualities,” Strategy Analytics notes in its Top 10 Internet of Things Trends for 2018.
Part of that process may be blockchain, but unlike some of the other experts we’ve been reading, Strategy Analytics is not completely enthusiastic about blockchain’s potential with regards to IoT. “Blockchain will be a key area to watch in 2018, due to enhanced security, supply chain, and smart contract applications. But we must remember that blockchain is still in its infancy.”
Peter Loop of Infosys, the author of a January 2018 Coindesk piece, is more enthusiastic. “With the rise of ransomware attacks demanding cryptocurrencies, blockchain, and IoT cybersecurity will emerge with defenses based on cryptocurrency technologies,” it predicts. “The need for a more secure blockchain-based identity approach, in which no one holds all the keys, will emerge.”
But let’s leave the final word to the one expert who’s quite bullish on blockchain’s potential: Yevgeny Dibrov, the author of the aforementioned Harvard Business Review piece:
“Solutions we’ve relied upon in the past, such as training employees, will not mitigate the massive security challenge companies are facing. The scope of IoT is far too complex,” he writes. “It’s time to remove people from the discussion and move towards a more intelligent, secure future.”





binance registrieren
May 15, 2023 at 4:56 AM
Your article helped me a lot, is there any more related content? Thanks! https://accounts.binance.com/de-CH/register?ref=FIHEGIZ8
spravki-kupit.ru
June 27, 2023 at 1:32 AM
проверенный диплом
June 27, 2023 at 10:06 PM
It’s really a cool and helpful piece of information. I’m satisfied that you simply shared this helpful info with us. Please stay us informed like this. Thank you for sharing.
гостиничные чеки купить спб
July 3, 2023 at 8:50 AM
Magnificent beat ! I wish to apprentice even as you amend your site, how can i subscribe for a blog site? The account aided me a appropriate deal. I have been tiny bit familiar of this your broadcast provided bright transparent concept
гостиничные документы санкт петербург
July 4, 2023 at 5:53 AM
Asking questions are truly pleasant thing if you are not understanding anything fully, but this post gives nice understanding even.
bezogoroda.ru
July 4, 2023 at 7:23 AM
I needed to thank you for this great read!! I certainly enjoyed every little bit of it. I have you book-marked to check out new stuff you post
casino chips singapore
July 5, 2023 at 9:14 AM
Appreciation to my father who shared with me about this weblog, this blog is in fact awesome.
daachka.ru
July 6, 2023 at 6:44 AM
These are really enormous ideas in regarding blogging. You have touched some nice factors here. Any way keep up wrinting.
daachka.ru
July 6, 2023 at 1:10 PM
You made some decent points there. I looked on the web for more info about the issue and found most individuals will go along with your views on this website.